Running a Tor Exit Node for fun and e-mails
September 2, 2016
The Tor Project is a non-profit organization in the United States that created Tor, The Onion Router, a free software that creates an open network of volunteers which helps people anonymize their traffic by routing it through three or more other computers before it reaches its final destination.
Tor got its name from the encryption that happens during the relaying of the information. Every time a user wants to access a website using Tor, they create a circuit between three or more nodes in the network. Afterwards, they encrypt the data with the last node’s public key, then they encrypt the output with the middle node’s public key, and finally they encrypt that output with the first node’s public key. This creates an message with several encryption layers, which needs to be peeled by each node like an onion.
In order to be able to use Tor, volunteers need to operate the so-called “Tor Relays”. These are computers running the Tor software that accept incoming connections and forward them to the next hop, or to the Internet.
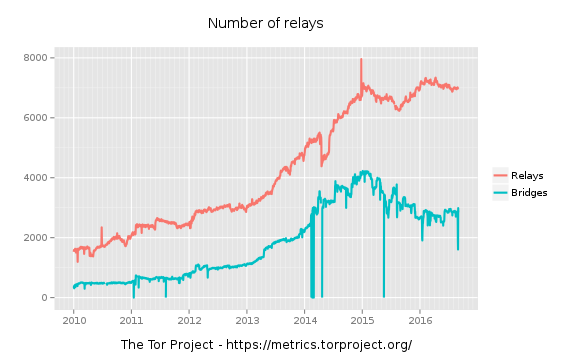
Currently there are approximately 7,000 relays in the network, a number that so far has kept increasing. The following graph is from the Tor Project Metrics Page which illustrates that:
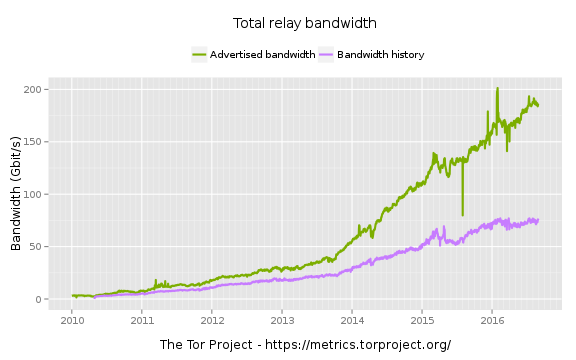
With those relays being mostly servers with very fast Internet connections, the total bandwidth available for Tor is currently 180 Gb/s, a very large number with today’s standards, especially for a volunteer, not-for-profit network. Again, Tor Project Metrics has the appropriate graph:
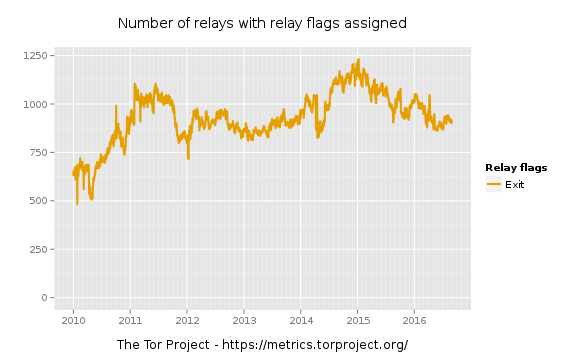
However, the way Tor works, not every node in the network relays traffic to and from the Internet. The subset of Tor relays that also provide access from within Tor to the Internet is called “Exit Nodes”, and, of course, it’s smaller than the total amount. Currently there are about 900 of these nodes:
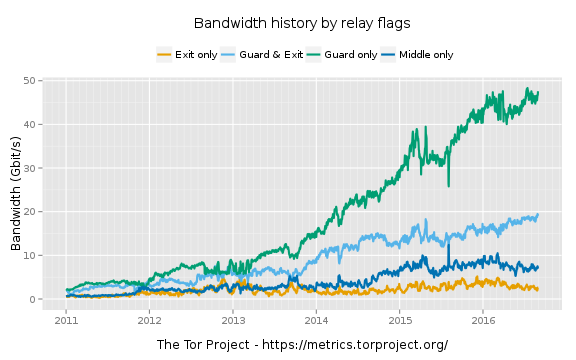
As you probably noticed by now, the above number of 180 Gb/s isn’t the total capacity of the Tor network since each connection consumes at least three times more bandwidth than needed, therefore Tor users can actually access the Internet with only one third of that, or 60 Gb/s, right? Well, not exactly. It all depends on the total bandwidth available by the Tor Exit Nodes: it doesn’t matter if the entire network can push 60 Gb/s if the total Exit Node bandwidth is 1 Gb/s. It will create a bottleneck for accessing the web.
Currently, the bandwidth of Exit-Only Relays is at a mere 2,5 Gb/s, while the bandwidth of Entry-Node and Exit-Node Relays is at about 7,5 Gb/s. That means the usable Exit bandwidth is around 5-10 Gb/s for the entire network:
Now you may be wondering why out of 180 Gb/s, only about 10 is available for access to the Internet. Why isn’t everyone marking their relay as exit node?
To understand the logistics behind running a Tor Exit Node, I will tell you how I got to run my Tor Exit Node for over 8 months. Hopefully, during the process, some of your questions will be answered, and you’ll also learn some new things. Please note that this is my personal experience and I cannot guarantee it will be the same for you. Also, I must state that I have run other exit nodes in the past, as well as multiple non-exit relays and bridges.
The first thing you need to understand is why people use Tor. The majority of Tor traffic is legitimate users accessing the web anonymously, through insecure networks like Public WiFi, etc. Another portion of the traffic is from journalists, dissidents, and others, in countries where the Internet is censored. Tor provides a gateway to the free Internet, bypassing most mediums of censorship that may be imposed by someone, like for example oppressive regimes. Other users of Tor are Governments and Law Enforcement who want to communicate securely and not expose their identities. Finally, just like with everything else, we have malicious users. Not necessarily highly skilled criminals, but people in general who (ab)use the anonymity that Tor provides to commit things they otherwise wouldn’t.
That last, tiny portion of users is the primary reason people don’t run more Exit Nodes. Some times, when an IP Address conducts an attack of any nature, the victims and/or any other intermediaries, contact the ISP of the attacker and ask them to prevent that in the future. If they fail to comply, additional measures are usually taken such as contacting the ISP’s ISPs and asking them to disconnect the abusive network from the Internet.
That means, that if you’re a server provider, you will probably prohibit your users from running Tor Exit Nodes, since at least a few of these e-mails will arrive probably within weeks, and you risk the reputation of your network. However, there are some open-minded ISPs that allow that, although they are not too many.
In addition to that, some operators are afraid of being contacted by the police, or even sued, for the actions of others using their node.
With that in mind, the first thing I had to do was find a host that allowed (or did not explicitly ban) Tor Exit Nodes. The fastest way to do this is to again use Tor Project Metrics. They have a special page which shows all the Exit Nodes grouped by their ISPs. As you can see, most people use OVH, ONLINE, LeaseWeb, as well as a few other ISPs. Although running a Tor Exit in these providers help, it’s good to have diversity in the network, so running in a smaller provider is probably a better choice.
After looking at several options, I went with KeyWeb. More specifically, I looked at their Virtual Servers, which start at just 4,90€. The model currently powering DevStaffCrete1 is “RVS M14”, which uses OpenVZ and runs on an Intel Core i5 Processor. It comes with 1 GB of RAM (minimum), 100 GB of SSD, as well as “unlimited bandwidth”.
The main thing you need to look for when getting a server is the available bandwidth. Tor consumes a lot of bandwidth relaying traffic, especially for Exit Nodes. The next, and probably last, thing is the CPU. It is not very important, but it’s good to have more cores, especially for higher speed relays.
I ordered that server with a monthly contract and after paying 4,90€ via PayPal, I had SSH access. The first thing I did was to delete everything that wasn’t needed. After finishing, the only processes that were running were init, kthreadd, khelper, systemd-networkd, systemd-udevd, systemd-journald, cron, systemd-resolved, and sshd. The next thing was to upgrade all packages and reboot. Then, I did a very basic rootkit check, and finally I installed tor from the Debian repositories.
The configuration file was pretty simple:
DataDirectory /var/lib/tor
ORPort 443
Address 62.141.55.117
OutboundBindAddress 62.141.55.117
Nickname DevStaffCrete1
RelayBandwidthRate 1 MB
RelayBandwidthBurst 1 MB
ContactInfo abuse@daknob.net || noc@daknob.net || tor@daknob.net
DirPort 80
DirPortFrontPage /etc/tor/tor-exit-notice.html
MyFamily A71E2F812280830ED6E73C380782A8172448A5F3
ExitPolicy reject 0.0.0.0/8:*
ExitPolicy reject 10.0.0.0/8:*
ExitPolicy reject 44.128.0.0/16:*
ExitPolicy reject 127.0.0.0/8:*
ExitPolicy reject 192.168.0.0/16:*
ExitPolicy reject 169.254.0.0/15:*
ExitPolicy reject 172.16.0.0/12:*
ExitPolicy reject 62.141.55.117:*
ExitPolicy reject 62.141.54.117:*
ExitPolicy reject *:25
ExitPolicy reject *:179
ExitPolicy accept *:*
I created a small HTML file that’s hosted on port 80 that contained some information about the host, and then I thought I should start a bandwidth rate-limit of 10 Mb/s, so as not to harm other colocated users.
As you can see, this Exit Policy is pretty lax. It only prevents access to private address space, as well as two ports, namely tcp/25 which is used for e-mail, so as to prevent spam coming from this IP Address, as well as tcp/179, which is used by BGP, and I wanted to avoid the exploitation of a particular vulnerability in KeyWeb ;-)
After a few days of operation, traffic started to flow through the Exit Node at a rate of 10 Mb/s, as specified in the configuration file. Since I wanted to make the most out of the available 100 Mb/s NIC, I started increasing the limit by 10 Mb/s every three days. This would allow me to see how much bandwidth I could push before receiving e-mails from KeyWeb and/or degrading others’ service.
After playing with it a little bit, I concluded that the best available rate limit is 50 Mb/s, utilizing half the server’s uplink. I think that’s a fair speed for 4,90€ / month.
By that time, I had a Tor Exit Node with a very lax Exit Policy, running at 50 Mb/s, for the cost of one or two coffees.
But it wasn’t over yet. This was back in January 2016. Since then, almost 8 months have passed. What happened during that time?
The first thing that I had to do twice a month is to ssh into the server and upgrade all packages to the latest version, or at least those not upgraded by unattended-upgrades. This is an important part of the process since it ensures the server is always up-to-date. Because there were too many TCP connections open, sometimes ssh and apt-get could not allocate a socket, and failed. For ssh, what I did was run this on my laptop:
while [ true ]; do ssh user@62.141.55.117; sleep 0.1; done
This is an infinite loop that ran for minutes sometimes until a socket was available and I was connected to the server. In order to run apt-get however, I wasn’t so lucky. The above trick did not work, and what I had to do was stop the tor service for a few minutes.
The second thing that happened was something I pretty much intended. Spammers crawled the three e-mail addresses in the Exit Node description, and started sending a couple of e-mails per day. Since tor@daknob.net is only used in this description, I could easily detect spam messages coming to abuse@ and noc@ because they would also arrive to tor@. I configured my mail server to automatically submit any and all attachments to tor@ to Virus Total so I can give the Antivirus companies free samples and help protect users against malware.
The final thing that happened was what I expected. Abuse e-mails started pouring in. Despite malicious users being the minority of Tor users, as an absolute number, there are many of them. In addition to that, the more time the relay is running, the more traffic is going through, and therefore the more e-mails you get, statistically speaking.
These e-mails are not something that should scare you: you need to politely reply to each and every one of them, letting the person contacting you know what’s going on, and always being available to help them further.
One of the types of e-mails you’ll get most often is for copyright infringement by users downloading movies via torrents. There are two primary companies that send these e-mails, “Irdeto USA, Inc.” and “IP-Echelon Pty. Ltd.”. All these e-mails are automated and are sent quite often. To save time replying to them, I also wrote a bot that would do just that. Every time I received an e-mail in abuse@daknob.net, I would scan for some common patterns, and then use Regular Expressions to get some fields of the message that were needed. Luckily, both companies followed a standard, namely ACNS XML, which made their e-mails easy to parse.
Afterwards, an automated reply was crafted, and then sent to their e-mail, automatically Bcc-ing me. The e-mail message was:
Dear $1,
I am responding to your ticket regarding abusive behavior for the IP Address $2 as a member of the server administration.
First of all, I’d like to thank you for reaching to us and reporting this behavior, since we also believe in the copyright law. Unfortunately, I am not able to further process your request because this IP Address is part of the Tor Network and more specifically it is an Exit Node. That means that we are routing anonymized, encrypted traffic from the Tor Network to the Internet without processing or filtering. We currently employ some tactics that help minimize abuse (such as block port 25). From your letter I can see that you claim this server is hosting copyrighted material, which is not the case. From what I can tell, no service can be hosted on this IP Address since it only relays outbound connections to the Internet. If you mean that the movie is pirated via BitTorrent, this could be the case but we currently cannot limit this.
Since we are a Service Provider that simply routes “client” traffic, and in this case cannot assist in the investigation due to the way Tor works, I do not see a way to help with this ticket. If you have any recommendations, please let us know so we can further discuss it.
For more information, please visit http://$2, a website hosted on the same server, with more details.
This helped process most incoming e-mails, however, everything else was handled manually. In some e-mails about copyright infringement that were not automatically replied to, I also added a bit of human touch: If the movie was good and I had seen it, I also let them know that their clients’ movie was pretty good.
Other e-mails I received about this particular node include, but are by far not limited to, Wordpress comment spam, port scanning, credential brute force attacks, attempted SQL Injections, WAF alerts, in no particular order.
In general, the experience of running a Tor Exit Node has been fun, and I was never contacted by any law enforcement agency, nor had anything negative happen to me in relation to that. The KeyWeb staff were very helpful and I recommend running an exit node or two there as well. The entire thing did not consume a lot of time and it certainly helped people out there, using Tor.
Finally, I’d like to add some statistics about the Exit Node so far:
- It has been running for almost 8 months
- It costs 4,90 EUR / month. In comparison, the same server in AWS would cost $1,122, or 992€ as of today
- The total cost to date is 40€. In comparison, the same server in AWS would cost about 8,000€.
- It is pushing up to 50 Mb/s, every second
- It relayed over 70 TB of Tor traffic
- It generated 2,729 Abuse E-Mails
- It is only blocking port 25, and this to prevent spam
- It helped hundreds or thousands of people to reach an uncensored Internet
- It helped even more people browse the Internet anonymously and with privacy
Do you want to run an Exit Node yourself? What are your concerns? What do you think about that? Let me know in the comments below.
Disclaimer:
The information provided in this blog post is for purely educational purposes and in order to document my experiences. I cannot guarantee that everything here will apply to you, or anyone else. All the information above should be treated as educational material. I take no responsibility for your actions and/or the results of your actions after following the advice above.